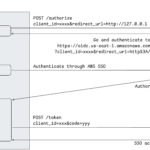
In 2021, I wrote about how offensive actors can leverage AWS SSO device code for phishing, rendering modern security controls like FIDO authentication or identity provider device posture ineffective: Phishing for AWS credentials via AWS SSO device code authentication. In this post, we’ll take a closer look at the newly-released PKCE support for AWS SSO authentication flows. A Short History of Device Code Phishing As highlighted in the original article, Device Code phishing isn’t new or specific to AWS. In fact, it had previously been demonstrated in the context of Azure AD. However, following the publication, the technique gained notableContinue reading… The New PKCE Authentication in AWS SSO Brings Hope (Mostly)
Tag: aws
IMDSv2 enforcement: coming to a region near you!
Cloud Security Breaches and Vulnerabilities: 2021 in Review
Privilege Escalation in AWS Elastic Kubernetes Service (EKS) by compromising the instance role of worker nodes
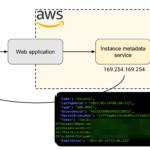
In this post, we discuss the risks of the AWS Instance Metadata service in AWS Elastic Kubernetes Service (EKS) clusters. In particular, we demonstrate that compromising a pod in the cluster can have disastrous consequences on resources in the AWS account if access to the Instance Metadata service is not explicitly blocked. Introduction For the purposes of this post, we’ll use an EKS cluster running Kubernetes v1.17.9 and created with eksctl. We could also have created the cluster using Terraform or CloudFormation. Once we created the cluster, we can use the AWS CLI to update our kubectl configuration file forContinue reading… Privilege Escalation in AWS Elastic Kubernetes Service (EKS) by compromising the instance role of worker nodes
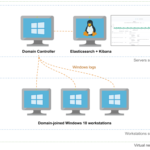
Automating the provisioning of Active Directory labs in Azure
Today, I’m releasing Adaz, a project aimed at automating the provisioning of hunting-oriented Active Directory labs in Azure. This post is the making of, where we walk through how to leverage Terraform and Ansible to spin up full-blown Active Directory environments with Windows Server 2019 and Windows 10 machines.
Abusing the AWS metadata service using SSRF vulnerabilities
I recently worked on a small toy project to execute untrusted Python code in Docker containers. This lead me to test several online code execution engines to see how they reacted to various attacks. While doing so, I found several interesting vulnerabilities in the code execution engine developed by Qualified, which is quite widely used including by websites like CodeWars or InterviewCake. The combination of being able to run code with network access and the fact that the infrastructure was running in Amazon Web Services lead to an interesting set of vulnerabilities which we present in this post.